Pwning Admin Panel To Change Movie Ticket Prices at Disney
Summary
This bug allowed me to access a Management Information System Portal by bruteforcing common passwords. The admin panel allows changing theatre names, theatre status, changing ticket prices, user management, viewing system logs, etc. in South Asian countries.
Reproduction Steps
- Find all the ASNs owned by The Walt Disney Company. Do enumeration to find more hosts using techniques described in my blogs.
- Take all the enumerated passive and active hosts and run a masscan at common http ports.
- Run httpx over all online hosts with status code, title, content type, etc. flags.
- Got a host with "Admin Panel" title name and login window.
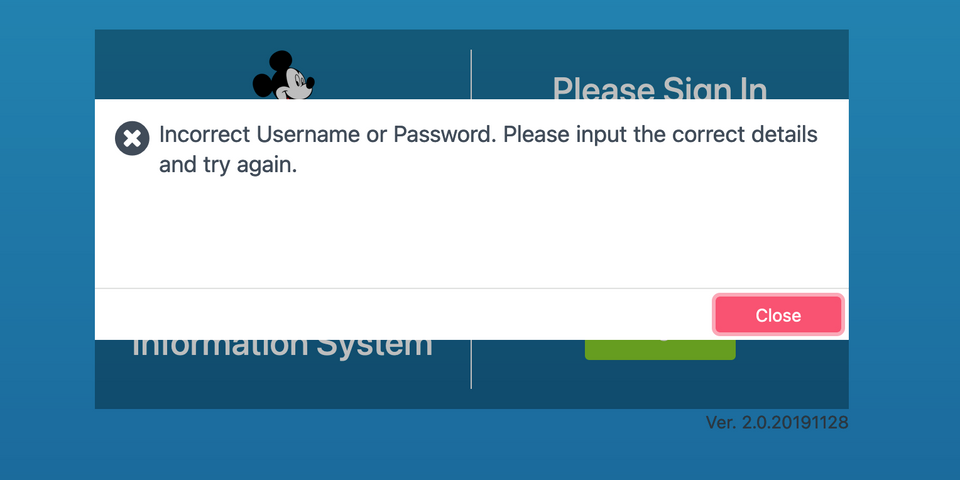
- Entered "admin" and "encodedguy" and got different responses that helped to figure out that admin is the available username in the portal.
- Entered 5 common passwords and got "5 fails, please wait 15 minutes...", but this error was only on the frontend and no server side protection was present.
- Sent the login request to Intruder and fuzzed for passwords with a wordlist of 20K common passwords (thanks to danielmiessler).
- Found this password "P@ssw0rd" with different content length.
- Logged in using "admin":"P@ssw0rd" and got access to the portal.
This portal manages Disney theatres for countries like Indonesia, Thailand, and South Asian countries. An attacker could have changed theatre prices in all theatres in one click, changed the user management, status of these theatres, etc.
Timeline
- 9 April 2022 – Report sent via Hackerone (The Walt Disney Company).
- 13 April 2022 – Report triaged by internal triager.
- 8 June 2022 – Retest completed and fix worked.
- 10 June 2022 – Report resolved and bug is not reproducible.
Happy Hacking!!