Cheatsheet - 15 Methods to Bypass 2FA Mechanism

In 2-Factor Authentication, when a user enters his password with the intention to log in the web application sends a temporary code to the user’s verified email address and when the user enters the code only then he will be able to interact with his account.

Many websites and organizations rely on single-factor authentication where a user can log into his account using only a password without any additional layer of security and validation. But as social engineering attacks have become more and more sophisticated there is a dire need for an extra layer of security like 2-factor authentication.
Let’s discuss different techniques for bypassing 2-Factor Authentication:
1. 2-Factor Authentication Code Leakage in Response:
At 2-Factor Authentication Code Triggering request, such as Send OTP functionality, capture the request.
See the response of this request and analyze if the 2-Factor Authentication Code is leaked.
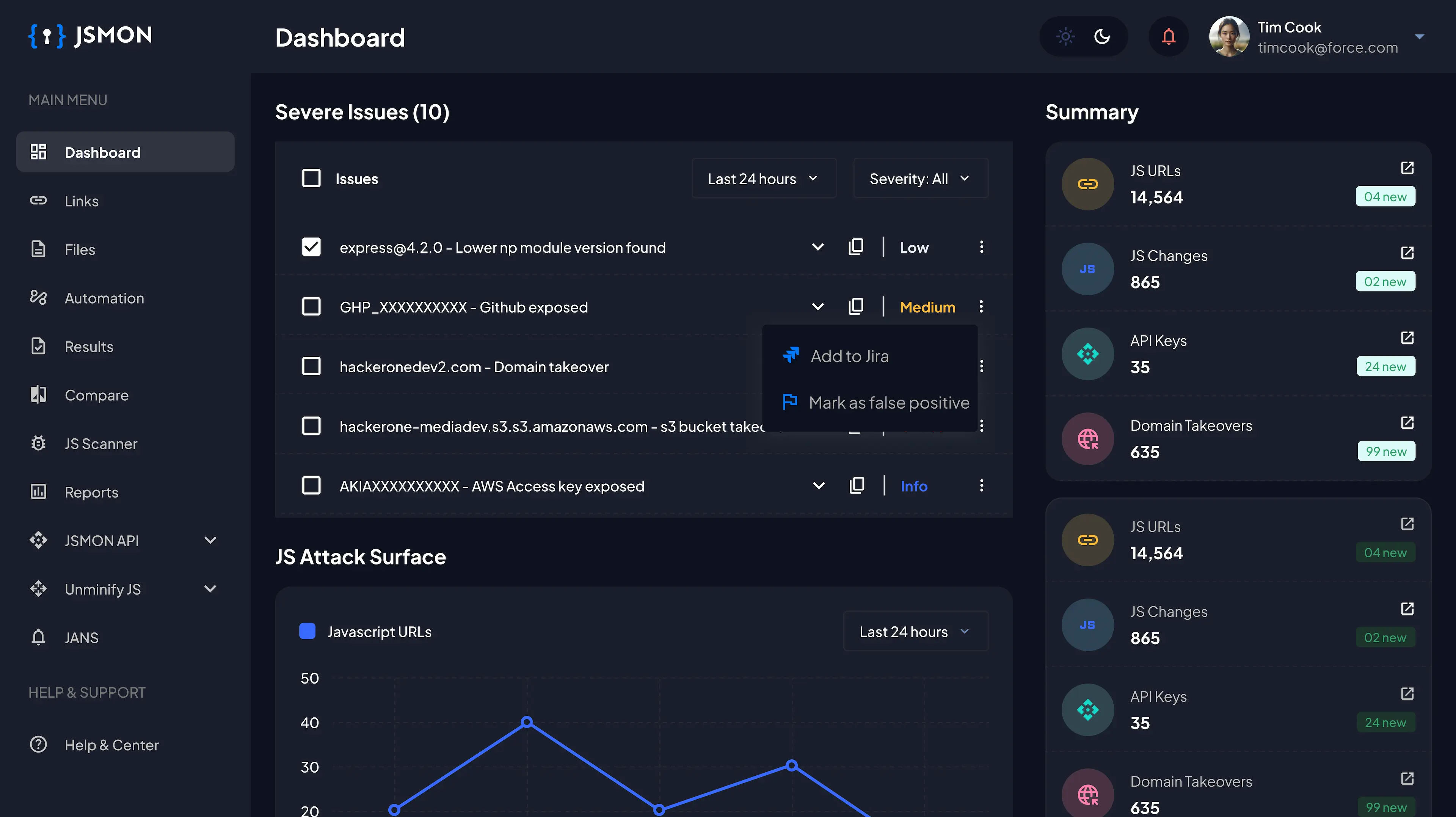
2. JS File Analysis:
While triggering the 2-Factor Authentication Code Request, Analyze all the JS Files that are referred to in response to see if any JS file contains information that can help bypass the 2FA code.
3. Lack of brute-Force Protection:
This involves all sorts of issues which comes under security misconfigurations such as lack of rate limit, no brute-force protection, etc.
Request a 2-Factor Authentication code and capture the request.
Repeat this request for 100–200 times and if there is no limitation set, that’s a rate limit issue.
At the 2-Factor Authentication Code Verification page, try to brute-force for valid 2-Factor Authentication and see if there is any success.
You can also try to initiate, requesting OTP at one side and brute-forcing at another side. At some point, the OTP will coincide and may give you a quick result.
4. Password Reset / Email Change — 2FA Disable:
Assuming that you are able to perform sophisticated phishing campaigns, force the end user to change the password.
2-Factor Authentication is disabled after the email is changed or the password is reset. This could be an issue for some organizations. However, it depends on a case-by-case basis.
5. Missing 2-Factor Authentication Code Integrity Validation:
Request a 2-Factor Authentication code from the attacker’s account.
Use this valid 2-Factor Authentication code in the victim 2FA Request and see if it bypasses the 2FA protection.
6. Direct Request:
Directly navigate to the page which comes after 2-Factor Authentication or any other authenticated page of the application and see if this bypasses the 2-Factor Authentication restrictions.
7. 2FA Refer Check Bypass:
Directly navigate to the page which comes after 2FA or any other authenticated page of the application.
If there is no success, change the refer header to the 2FA page URL. This may fool the application to pretend as if the request came after satisfying the 2FA condition.
8. Backup Code Abuse:
Apply the same techniques used on 2FA such as Response/Status Code Manipulation, brute force, etc. to bypass backup codes and disable/reset 2FA.
9. Enabling 2-Factor Authentication Doesn’t Expire Previous Session:
Log in to the application in two different browsers and enable 2FA from 1st session.
Use 2nd session and if it is not expired, it could be an issue if there is an insufficient session expiration issue. In this scenario, if an attacker hijacks an active session before 2-Factor Authentication, it is possible to carry out all functions without a need for 2-Factor Authentication.
10. Clickjacking on 2FA Disable Feature:
Try to iframe the page where the application allows a user to disable 2-Factor Authentication.
If the iframe attack vector is successful, try to perform a social engineering attack to manipulate the victim to fall into your trap.
11. Response Manipulation:
Check the response of the 2FA Request.
If you observe “Success”: false, change this to “Success”: true and see if it bypasses the 2FA.
You can also use Burp “Match & Replace” rules for this.
12. Status Code Manipulation:
If the Response Status Code is 4xx like 401, 402, etc.
Change the response Status Code to “200 OK” and see if it bypasses the 2FA.
13. 2-Factor Authentication Code Reusability:
Request a 2FA code and use it.
Now, re-use the same 2FA code in another session and if it is authenticated successfully, that’s a potential issue.
Also, try requesting multiple 2FA codes, and see if previously requested codes expire or not when a new code is requested.
Also, try to re-use the previously used code after a long time duration i.e 1 day or more. If it is successful, that is an issue since 1 day is more than enough for a sophisticated hacker to either brute-force or crack a 6-digit 2FA Code.
14. CSRF on 2FA Disable Feature:
Navigate to 2FA Page and click on “Disable 2FA” and capture this request with Burp Suite & generate a CSRF PoC.
Send this PoC to the victim, check if CSRF happens successfully and remove the 2FA from the victim's account.
Also, check if there is any authentication confirmation such as a password or 2FA code required before disabling 2FA.
Thank you for reading !!